AI-Powered Cybercrime Surges Globally as Ransomware Victims Jump 389%: Fortinet Report

Fortinet’s latest Global Threat Landscape Report warns that cybercriminals are increasingly deploying AI-driven tools to accelerate attacks, shrink exploitation timelines and industrialize cybercrime operations across sectors worldwide.
Fortinet has sounded a stark warning over the rapid evolution of AI-enabled cybercrime, revealing that ransomware victims worldwide surged by 389% year-on-year as malicious actors increasingly weaponized artificial intelligence to execute faster and more sophisticated attacks.
Released by FortiGuard Labs, the company’s 2026 Global Threat Landscape Report paints a picture of cybercrime evolving into a highly organized ecosystem where hackers, access brokers and automated “shadow agents” operate across a streamlined attack lifecycle.
According to the report, cybercriminals are dramatically compressing the “time-to-exploit” window, with critical vulnerabilities now being weaponized within 24 to 48 hours — significantly faster than the 4.76-day average recorded in earlier reports. In some cases, exploitation attempts were observed within hours of public vulnerability disclosures.
The report identified 7,831 confirmed ransomware victims globally during 2025, compared to nearly 1,600 victims in the previous year. Manufacturing, business services and retail emerged as the most targeted sectors, while the United States, Canada and Germany recorded the highest concentration of victims.
Fortinet attributed the surge partly to the growing availability of AI-powered cybercrime kits such as WormGPT, FraudGPT and BruteForceAI, which are lowering technical barriers for attackers while improving attack efficiency.
Derek Manky, Chief Security Strategist and Global VP of Threat Intelligence, Fortinet FortiGuard Labs. said, “Cybercrime is one of the world’s most pervasive and costly threats, and our latest Global Threat Landscape Report reveals how malicious actors are beginning to leverage agentic AI to execute more sophisticated attacks. As cybercriminals increasingly use AI to bolster their tactics, cyber defenders must evolve cybersecurity operations into an industrialized defense and adopt AI-enabled tools that respond at the same velocity as modern threats.”
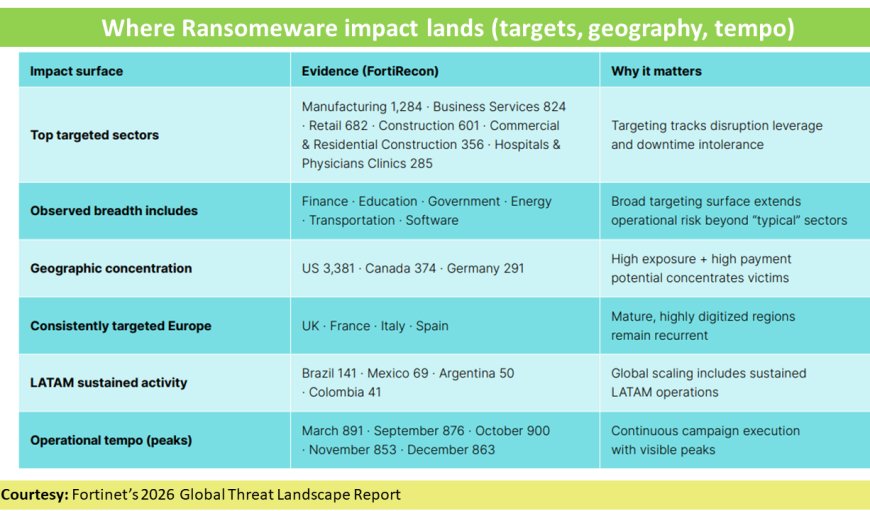
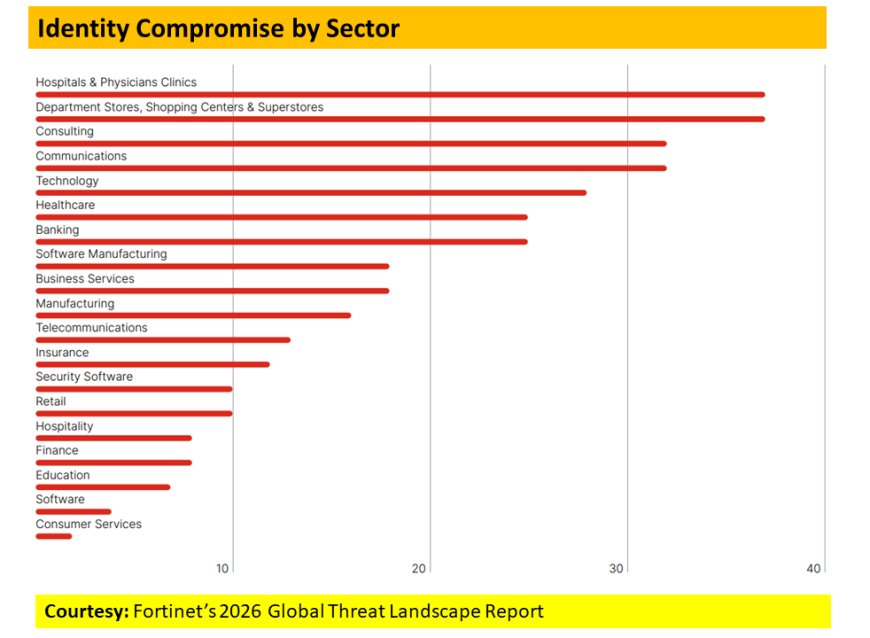
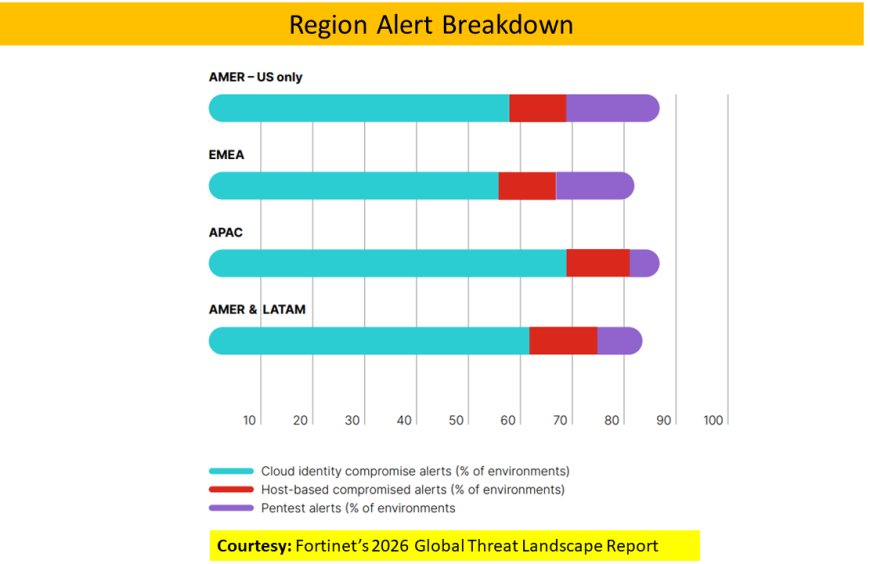
The report also highlighted a growing shift toward identity-based attacks and stolen datasets. FortiGuard Labs found that most cloud-related incidents in 2025 originated from exposed or misused credentials rather than direct infrastructure exploitation. Hospitals, physician clinics and retail establishments were among the most vulnerable sectors due to complex cloud integrations and large identity ecosystems.
Interestingly, while brute force attempts declined by 22% year-on-year, Fortinet noted that attackers are now relying on smarter, AI-optimized intrusion methods that require fewer attempts but deliver higher success rates. At the same time, global exploitation attempts increased by over 25%, reflecting growing efficiency in cyberattack strategies.
Credential-stealing malware also remained a major threat vector, with RedLine, Lumma and Vidar malware families dominating global infection trends. The report noted that “stealer logs” — datasets containing credentials alongside browser and identity information — are increasingly preferred by cybercriminals because they allow faster compromise and monetization.
Beyond threat detection, Fortinet highlighted its role in global cybercrime disruption efforts, including support for INTERPOL-led operations such as Operation Red Card 2.0 and Operation Serengeti 2.0 through the World Economic Forum’s Cybercrime Atlas initiative.
As cyber threats become more automated and interconnected, Fortinet stressed that organizations must strengthen cyber resilience through AI-enabled defense systems, real-time threat intelligence and collaborative global response mechanisms to keep pace with an increasingly industrialized cybercrime economy.



 Editor
Editor