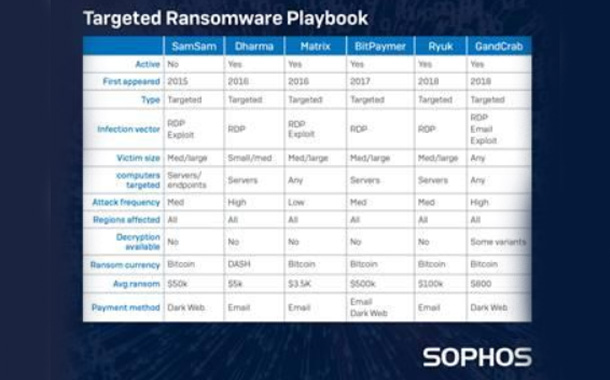
Sophos, released a new report about a ransomware family called Matrix. The malware has been operating since 2016 and Sophos has tracked 96 samples in the wild. Like previous targeted ransomware, including BitPaymer, Dharma and SamSam, the attackers who are infecting computers with Matrix have been breaking in to enterprise networks and infecting those computers over Remote Desktop Protocol (RDP), a built-in remote access tool for Windows computers. However, unlike these other ransomware families, Matrix only targets a single machine on the network, rather than spreading widely through an organization.
In its latest paper, SophosLabs reverse engineered the evolving code and techniques employed by the attackers, as well as the methods and ransom notes used to attempt to extract money from victims. The Matrix criminals evolved their attack parameters over time, with new files and scripts added to deploy different tasks and payloads onto the network.
Matrix ransom notes are embedded in the attack code, but victims don’t know how much they must pay until they contact the attackers. For most of Matrix’s existence, the authors used a cryptographically-protected anonymous instant messaging service, called bitmsg.me, but that service has now been discontinued and the authors have reverted to using normal email accounts. The threat actors behind Matrix make their demand for cryptocurrency ransom in the form of a U.S. dollar value equivalent. This is unusual as demands for cryptocurrency normally come as a specific value in cryptocurrency, not the dollar equivalent. It’s unclear whether the ransom demand is a deliberate attempt at misdirection, or just an attempt to surf wildly fluctuating cryptocurrency exchange rates.
Sophos recommends implementing the following four security measures immediately:
- Restrict access to remote control applications such as Remote Desktop (RDP) and VNC
- Complete, regular vulnerability scans and penetration tests across the network; if you haven’t followed through on recent pen-testing reports, do it now. If you don’t heed the advice of your pentesters, the cybercriminals will win
- Multi-factor authentication for sensitive internal systems, even for employees on the LAN or VPN
- Create back-ups that are offline and offsite, and develop a disaster recovery plan that covers the restoration of data and systems for whole organizations, all at once